Securing Autonomy: Applying the Agent Permission Protocol (APP) to LangGraph Patterns
Crittora Team
Feb 7, 2026
Tags:
TL;DR
Analyze common LangGraph design patterns through the lens of APP compliance, with practical risks and enforcement recommendations.
Key Takeaways
- Analyze common LangGraph design patterns through the lens of APP compliance, with practical risks and enforcement recommendations.
- Field note by Crittora Team, published Feb 7, 2026.
- Topics covered: agent permission protocol, langgraph, ambient authority, agent security.
Quick Answers
What is this article about?
Analyze common LangGraph design patterns through the lens of APP compliance, with practical risks and enforcement recommendations.
Who published this and when?
Crittora Team published this field note on Feb 7, 2026.
Is this available in multiple languages?
Yes. This page is the English version. A Spanish version is available at /es/field-notes/securing-autonomy-applying-the-agent-permission-protocol-app-to-langgraph-patterns.
Securing Autonomy: Applying the Agent Permission Protocol (APP) to LangGraph Patterns
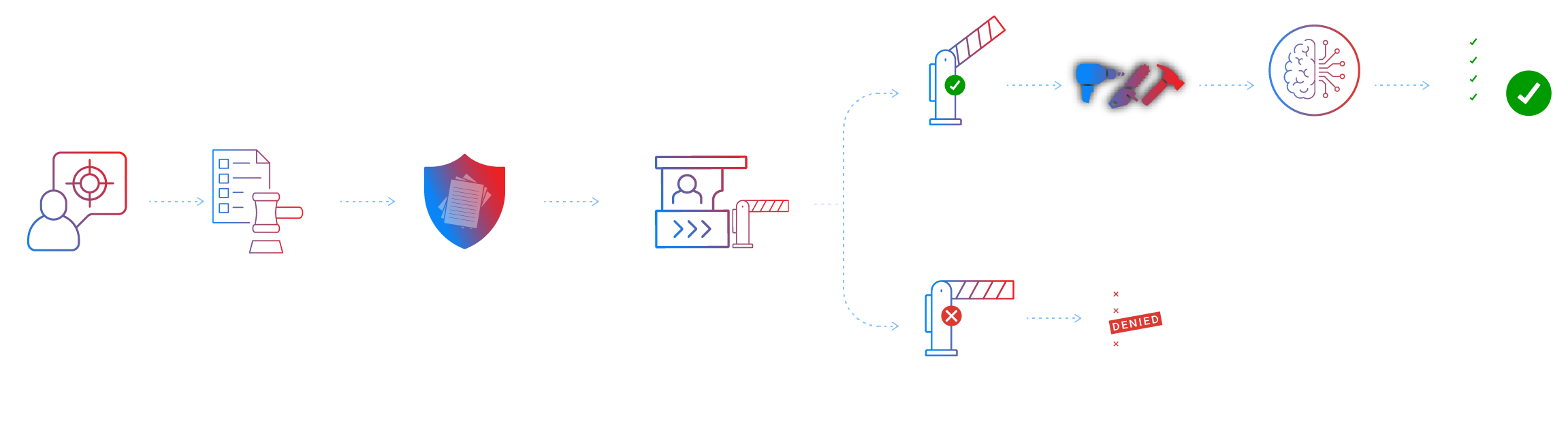
At Crittora, we believe that authority is the true boundary in agentic execution. While frameworks like LangGraph provide the structural elegance to build complex multi-agent workflows, they often rely on ambient authority—where any tool mounted in the runtime is implicitly available to the agent.
Without an explicit authority layer, even the most sophisticated LangGraph pattern is insecure by construction because it relies on model compliance rather than cryptographic enforcement. Below, we analyze common LangGraph design patterns through the lens of APP compliance.
1. Prompt Chaining: Verifying Intent at Every Link
The Pattern: Breaking a complex task into a sequence of LLM calls, where the output of one node is the input for the next.
The APP Lens: In a standard chain, authority is often granted once at the start. APP requires that each link in the chain presents a sealed permission policy.
Finding: Static chains often inherit broad permissions from the initial trigger.
Risk: Privilege Creep. If Node A needs read-only access but Node C needs write access, a single leaked credential grants the entire chain excessive power.
Recommendation: Use Time-Bounded Authority. Each node in the LangGraph should receive a unique, short-lived policy specifying the exact scope (capabilities) required for that specific step.
2. Routing: The “Confused Deputy” Trap
The Pattern: A router node uses an LLM to decide which downstream worker or tool to invoke based on user intent.
The APP Lens: Routing decisions are intelligence, not authority. A router proposing an action does not mean that action is authorized.
Finding: Routers often act as a Confused Deputy, where an agent acts on behalf of a user but invokes a tool the user did not explicitly authorize for that context.
Risk: The router may be manipulated via prompt injection to route to a sensitive tool (e.g., delete_database) that was mounted but not intended for the current request.
Recommendation: Implement Audience Binding. The APP verifier must ensure the Audience field in the policy matches the specific agent node attempting the execution.
3. Parallelization: Atomic Enforcement at Scale
The Pattern: Forking a workflow to execute multiple tool calls or agent tasks simultaneously.
The APP Lens: Each parallel branch must be treated as an independent execution event.
Finding: Parallelized workers often share the same ambient environment, making it impossible to audit which branch performed which action.
Risk: Unverifiable Audit Trails. If multiple tools are called simultaneously, traditional logs may not prove which specific policy authorized which specific side effect.
Recommendation: Deterministic Verification. Every parallel branch must present its own sealed policy to the APP Verifier before execution.
APP Compliance Checklist for LangGraph Developers
To move from experimental to production-ready, your LangGraph agents should meet these mandatory APP requirements:
| Requirement | Description | APP Reference | | --- | --- | --- | | Fail-Closed | Any failure in policy parsing or signature verification results in immediate denial. | | | No Ambient Authority | Tools must not be pre-mounted. They are only exposed after a policy is verified. | | | Cryptographic Sealing | Policies must be signed (Ed25519) and encrypted (X25519). | | | Explicit Intent | Every policy must encode the specific purpose (Intent) for the grant. | |
Conclusion: Intelligence is not Authority
LangGraph is a powerful engine for agent intelligence, but APP is the necessary brakes and steering. By separating the reasoning of the model from the authority to act, we enable a future where autonomous systems are both highly capable and provably safe.
Would you like me to review a specific LangGraph .py implementation to identify where the APP verification layer should be inserted?